
Keys to Cybersecurity
Welcome to the Keys to Cybersecurity! These are self-paced, engaging activities designed to introduce students in 3rd - 8th grades to basic cybersecurity concepts. After completing each Key, students will be awarded a certificate showing mastery over the topic!
Personally Identifiable Information (3-5)
First, you will learn what a digital footprint and personally identifiable information are. Then, you will learn when it is safe to share personally identifiable information and whom you should share it with.
Online Safety (3-5)
In this lesson, you will learn about some things to watch out for when using technology and how to best respond to those threats. You will also learn why it is important not to post private information online.

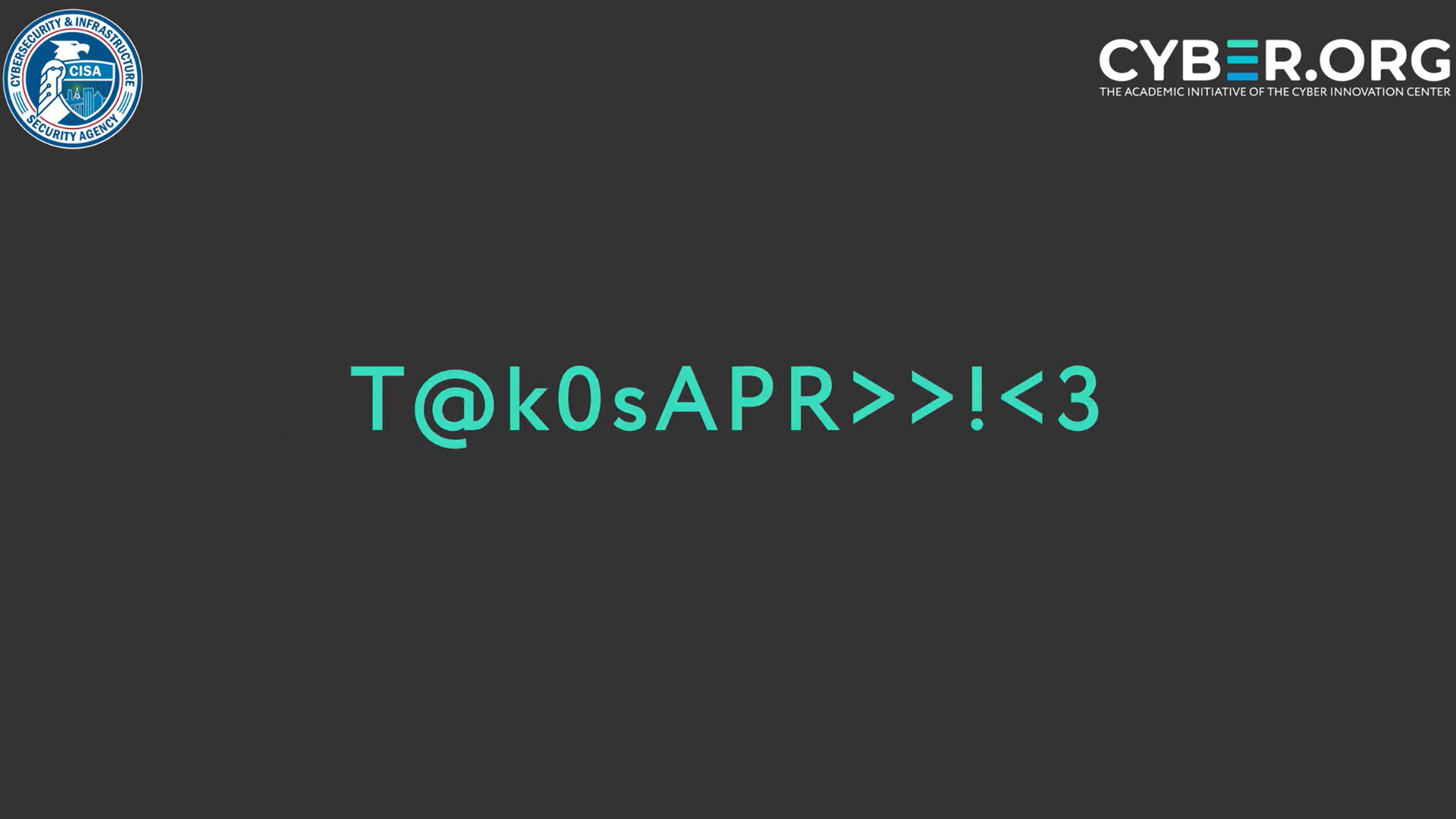
Authentication (3-5)
In this key, you will learn how to create strong passwords. You will also discover why it’s important to use multiple ways to protect your devices and learn about different kinds of authentication.

Connected Devices (3-5)
In this key, you will learn about the risks involved in opening unknown files and connecting to unknown devices. You will also discover the benefits of keeping your apps and devices updated and backing up data regularly. Additionally, you will learn about the Internet of Things (IoT).

Protecting your Digital Footprint (6-8)
First, you will learn about the many ways information is gathered about you online and how the information you put online stays there—even if you delete it! Then, you will learn how to limit access to authorized users. Finally, you will learn about some of the risks and benefits of sharing personally identifiable information (PII).

Online Threats and Vulnerabilities (6-8)
In this key, you will learn to identify the characteristics of an email or text message that may be part of a phishing scam. You will also become more aware of the different types of threats and vulnerabilities.
Defense in Depth (6-8)
You will learn how authentication and authorization methods can protect authorized users. You will also learn various strategies that can help protect simple networks.

Protecting Connected Devices (6-8)
For this key, you will learn how to protect your devices and files when using interconnected systems like the Internet of Things (IoT).
You will learn about the risks and benefits of IoT devices, the importance of file backups, and hardware and software vulnerabilities.
Explore our cybersecurity career profiles to learn what kind of jobs protect people from cyber criminals and cyber attacks!